Thank you for reading the LinuxSecurity Linux Advisory Watch newsletter! Staying on top of the latest security advisories is essential in maintaining an updated, secure Linux system. Our weekly newsletter is an easy, convenient way to track the security updates available for the software and applications you are using - helping you keep your Linux environment safe from malware and other exploits.
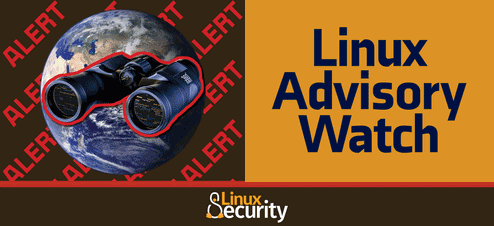
This week, important updates have been issued for Polkit, PostgreSQL and Squid:
Polkit
|
PostgreSQL
|
Squid
|
We recommend that you visit our Advisories page frequently to see the latest security advisories that have been issued by your Linux distro(s). We also now offer the ability to personalize your LinuxSecurity.com User Profile to include the latest advisories for the distros you select.
On behalf of the LinuxSecurity.com administrative team, I would like to extend a warm welcome to our newly redesigned site!
Yours in Open Source,